Relentless hackers abandon Windows to target your Apple ID
If there’s one thing that has become clear over the past year, it’s that Apple devices are not as secure as the company wants you to believe.
We’re four months into 2025 and there have already been over 10 instances in which attackers specifically targeted Apple users, and these are just the incidents we know of.
I’ll admit no device is foolproof, but there seems to be a growing trend where bad actors prefer targeting Apple users over other platforms. In fact, security researchers have recently identified a new phishing campaign in which hackers, who previously focused on Windows, are now setting their sights on Apple IDs.
STAY PROTECTED & INFORMED! GET SECURITY ALERTS & EXPERT TECH TIPS – SIGN UP FOR KURT’S ‘THE CYBERGUY REPORT’ NOW
A person working on an Apple laptop (Kurt “CyberGuy” Knutsson)
What you need to know
Security researchers at LayerX Labs have uncovered a new phishing campaign that specifically targets Mac users, marking a shift from its previous focus on Windows. The attackers initially lured Windows users with fake Microsoft security alerts designed to steal login credentials. However, after Microsoft, Chrome and Firefox implemented new security features to block these attacks, the hackers started redirecting their efforts toward Mac users instead.
The new attack closely mirrors its predecessor but with key modifications. The phishing pages have been redesigned to resemble Apple’s security warnings, making them appear legitimate to macOS users. The attack code has also been adjusted to specifically detect macOS and Safari users, ensuring that only Apple users see the fraudulent pages.
Plus, despite shifting their focus, the attackers continue to host these phishing pages on Microsoft’s Windows[.]net domain. Since this is a trusted Microsoft platform, it allows the phishing pages to evade detection by security tools that assess risk based on domain reputation.
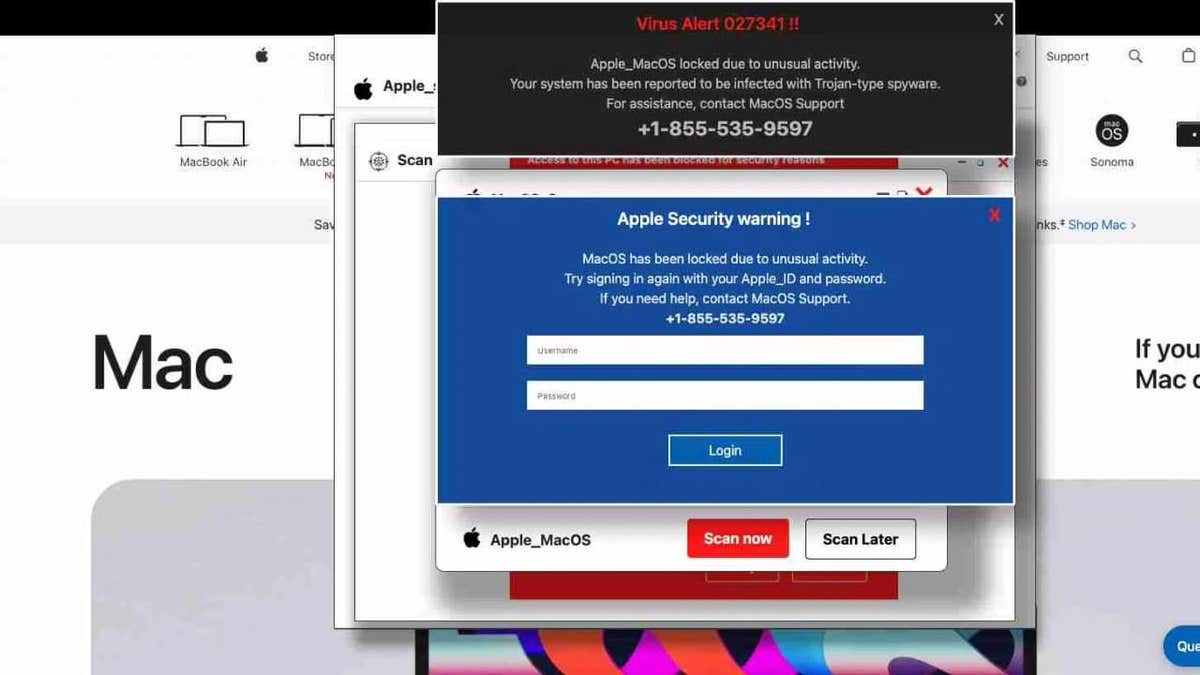
Compromised websites displaying fake security warning (LayerX)
FBI WARNS OF DANGEROUS NEW ‘SMISHING’ SCAM TARGETING YOUR PHONE
How victims are lured in
The phishing campaign exploits common yet highly effective methods called typosquatting and malicious redirects. Victims often end up on these phishing pages after making a simple mistake, such as mistyping a URL while trying to visit a legitimate website.
Instead of reaching the intended site, they land on a compromised domain parking page. From there, they are redirected through multiple websites before ultimately arriving at the phishing page, which presents a fake Apple security warning. Believing their Apple ID is at risk, victims are tricked into entering their credentials, unknowingly handing them over to the attackers.
One notable case involved a person using Safari who was working at a business secured by a Secure Web Gateway. Despite the organization’s security measures, the phishing attempt managed to bypass the gateway’s protections.
WHAT IS ARTIFICIAL INTELLIGENCE (AI)?

Compromised websites displaying fake security warning (LayerX)
APPLE’S IOS VULNERABILITY EXPOSES IPHONES TO STEALTHY HACKER ATTACKS
7 ways to stay safe from attackers targeting Apple users
Phishing campaigns are increasingly targeting macOS users, but you’re not defenseless. Here are four essential steps to protect yourself.
1. Use strong antivirus software: A reliable antivirus program is your first line of defense against phishing attempts and malicious websites. While Apple’s built-in security features provide some protection, they aren’t foolproof, especially against sophisticated phishing attacks that mimic legitimate Apple warnings. A robust antivirus solution can detect and block malicious sites before you even reach them, preventing you from accidentally entering your credentials on a fraudulent page. Additionally, advanced security software can identify suspicious redirects and alert you before you fall victim to typosquatting traps. Get my picks for the best 2025 antivirus protection winners for your Windows, Mac, Android and iOS devices.
2. Keep your software up to date: Regular updates to macOS and your applications aren’t just about new features. They’re critical patches that fix security vulnerabilities. Attackers are quick to exploit any weakness, so ensuring your operating system and all installed software are current minimizes the risk of a breach. Enable automatic updates where possible so you’re always protected by the latest security enhancements.
3. Regularly monitor your Apple ID activity: Even with strong security measures in place, it’s important to keep an eye on your Apple ID account for any signs of unauthorized access. Apple allows users to review their account activity, including devices logged into the account and recent changes. Regularly check your Apple ID settings to ensure that only trusted devices are connected and that no suspicious activity has occurred. If you notice anything unusual, such as login attempts from unfamiliar locations, immediately change your password and remove unauthorized devices. This proactive approach can help you catch potential breaches early and minimize damage.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
4. Enable two-factor authentication (2FA): Strong, unique passwords for every account are essential, but they’re even more effective when combined with two-factor authentication. Even if attackers manage to steal your credentials through a phishing attack, 2FA adds an extra barrier that makes unauthorized access significantly harder. Consider using a password manager to generate and store complex passwords. Get more details about my best expert-reviewed password managers of 2025 here.
5. Use a recovery key for enhanced security: Apple offers an optional feature called a recovery key, which is a 28-character code that provides an extra layer of security for your Apple ID. When you enable a recovery key, Apple disables its standard account recovery process, meaning you’ll need this key, along with access to a trusted device or phone number, to reset your password or regain access to your account. This makes it significantly harder for attackers to take control of your account.
To set up a recovery key, go to Settings > [Your Name] > Sign-in & Security > Recovery Key on your iPhone, iPad or Mac. Follow the prompts to generate and confirm your recovery key. Be sure to write it down and store it in a secure location, such as a safe or with a trusted family member. Keep in mind that losing both your recovery key and access to trusted devices can permanently lock you out of your account. However, if used responsibly, this feature gives you greater control over your account’s security.
6. Enable biometric authentication: Apple devices offer advanced biometric authentication options like Face ID and Touch ID, which provide an extra layer of security. These features make it significantly harder for attackers to gain access to your device or sensitive accounts, even if they manage to steal your credentials. Enable biometric authentication wherever possible, especially for apps and services that store personal or financial information. Since biometric data is unique to you, it adds a level of protection that passwords alone cannot provide.
7. Practice safe browsing: Many attacks rely on simple user mistakes, such as mistyping a URL or clicking on suspicious links. Always verify that you’re visiting legitimate websites before entering any personal information. Be skeptical of unexpected security alerts, even if they mimic Apple’s design. Learning to identify the subtle signs of phishing, like unusual URL structures or generic greetings, can help you avoid falling for these scams.
HOW TO PROTECT YOUR IPHONE & IPAD FROM MALWARE
Kurt’s key takeaways
Apple has long sold the idea that its ecosystem is inherently safer than the alternatives, but that claim is starting to wear thin. The reality is that attackers are no longer ignoring Mac users, they’re actively targeting them, and Apple’s response has been anything but proactive. While Microsoft, Google and others roll out new security measures to counter evolving threats, Apple remains slow to adapt, relying on outdated assumptions about its platform’s safety.
CLICK HERE TO GET THE FOX NEWS APP
Do you believe Apple should be more transparent about security vulnerabilities affecting its users? Let us know by writing us at Cyberguy.com/Contact.
For more of my tech tips and security alerts, subscribe to my free CyberGuy Report Newsletter by heading to Cyberguy.com/Newsletter.
Ask Kurt a question or let us know what stories you’d like us to cover.
Follow Kurt on his social channels:
Answers to the most-asked CyberGuy questions:
New from Kurt:
Copyright 2025 CyberGuy.com. All rights reserved.
